Cisco Unified Communications Manager allows for very granular assignment of permissions, using the concept of roles and groups to assign specific permissions to users. A role is a list of permissions around a function, and a group is a list of roles, which can then be assigned to a user.
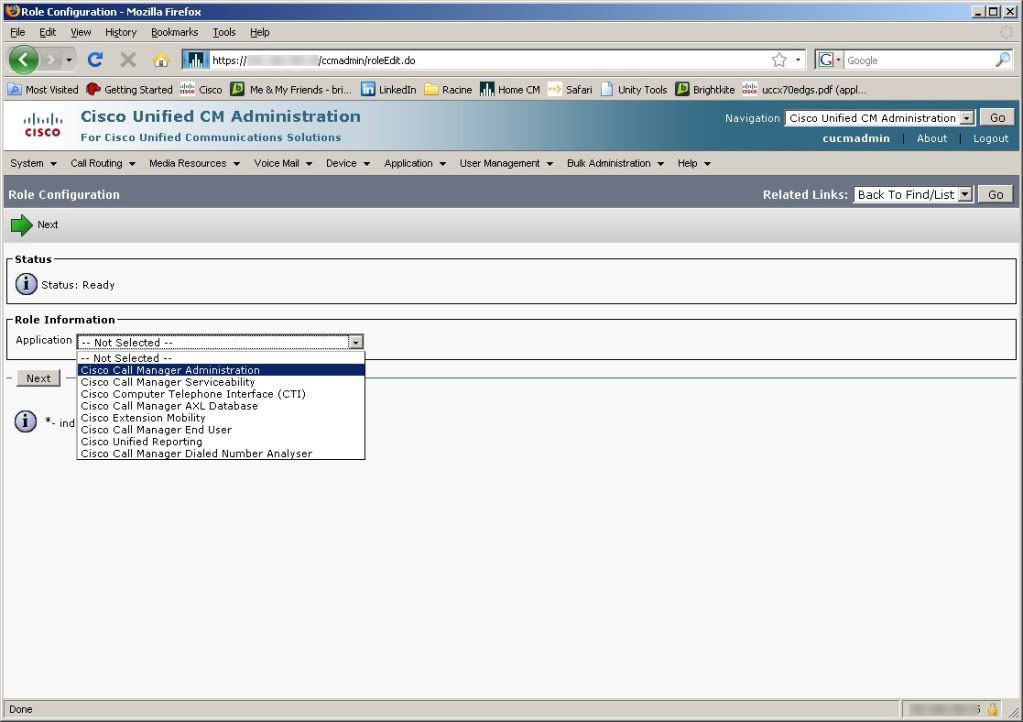
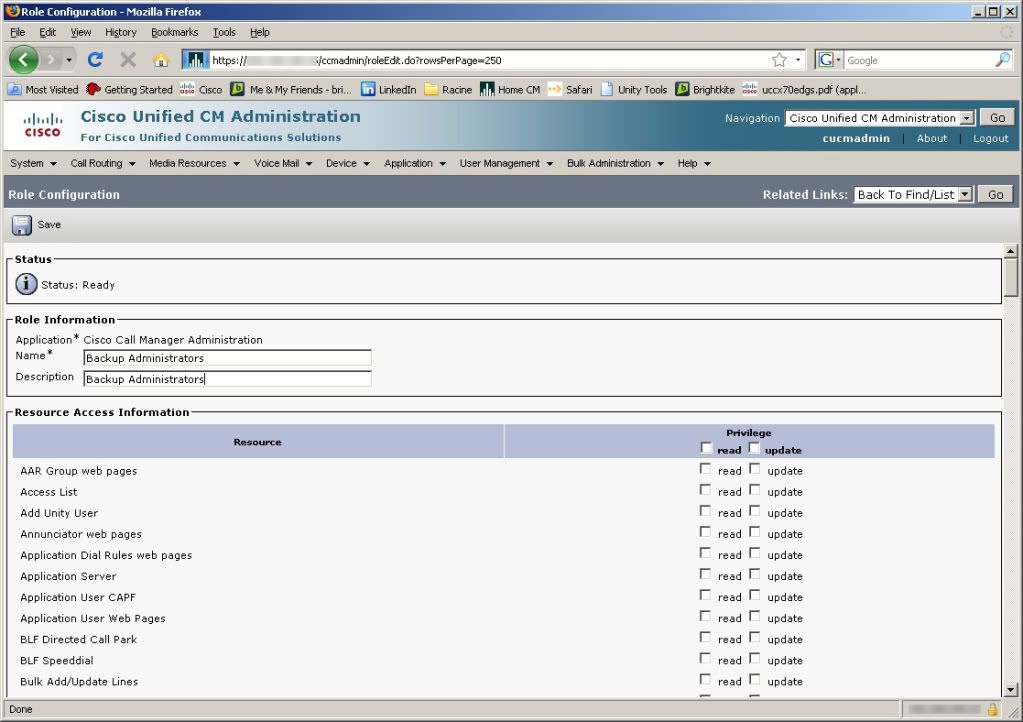
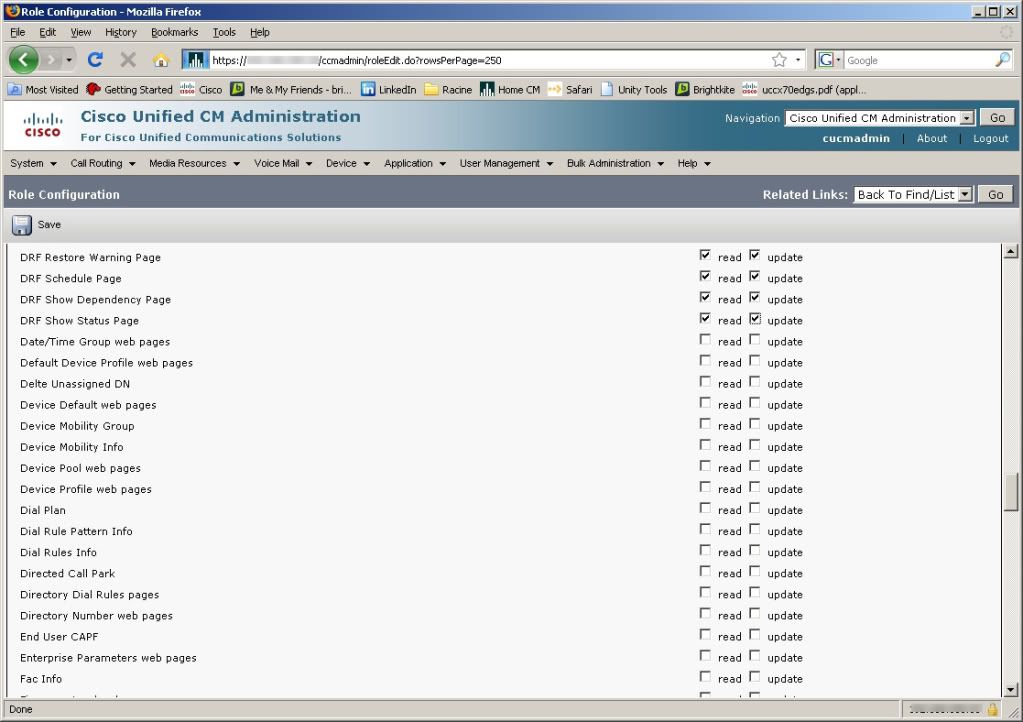
Permissions are assigned to Roles. An example of a role might be “Backup Administrator,” with permissions like “DRF Restore Warning Page,” “DRF Schedule Page,” “DRF Show Dependency Page,” and “DRF Show Status Page.” A role is specific to an application group, such as Cisco Unified Reporting, Cisco Call Manager Serviceability, or Cisco Call Manager Administration.
Permissions can include Read and Update, so a user could be given rights to view configuration elements, but not update them. This could be useful for auditing purposes, or for users that may need to verify a configuration, but not change it, such as a helpdesk user.
An Access Control Group contains a list of Roles. An Access Control Group might be something like “OS Administrators” which could include Roles like “Backup Administrator,” “LDAP Administrator,” etc. While a Role is specific to an Application, an Access Control Group can contain Roles from different Applications to create a comprehensive list of permissions, while limiting the number of groups a user must be assigned to to properly do their job.
Users are assigned to groups either in End Users configuration or in Access Control Group Configuration. Configuring in End User configuration is usually more efficient at assigning multiple groups to a user, while Access Control Group Configuration is going to be better for assigning multiple users to a single group.
Although you can see roles assigned to an end user in the End User Configuration Page, roles are not assigned directly to users. Users are assigned to groups, which contain roles, and the roles contain specific permissions within an application.
Configuration example after the fold.
Configuring Roles and Groups
Create a Role
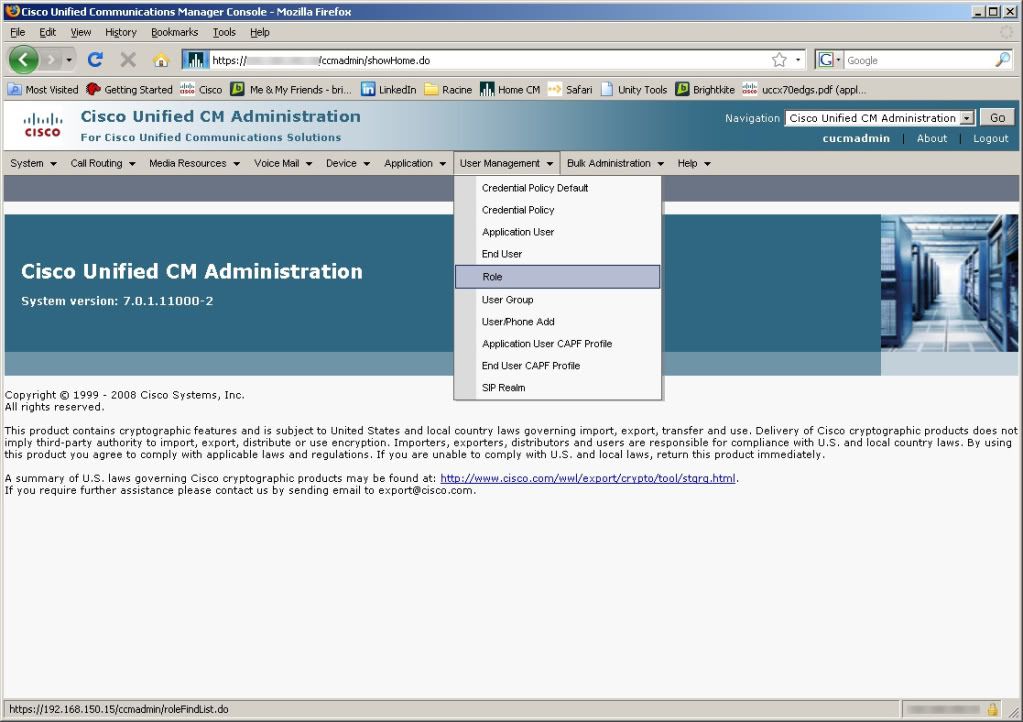
Select Role from the User Management menu in CUCM Administration
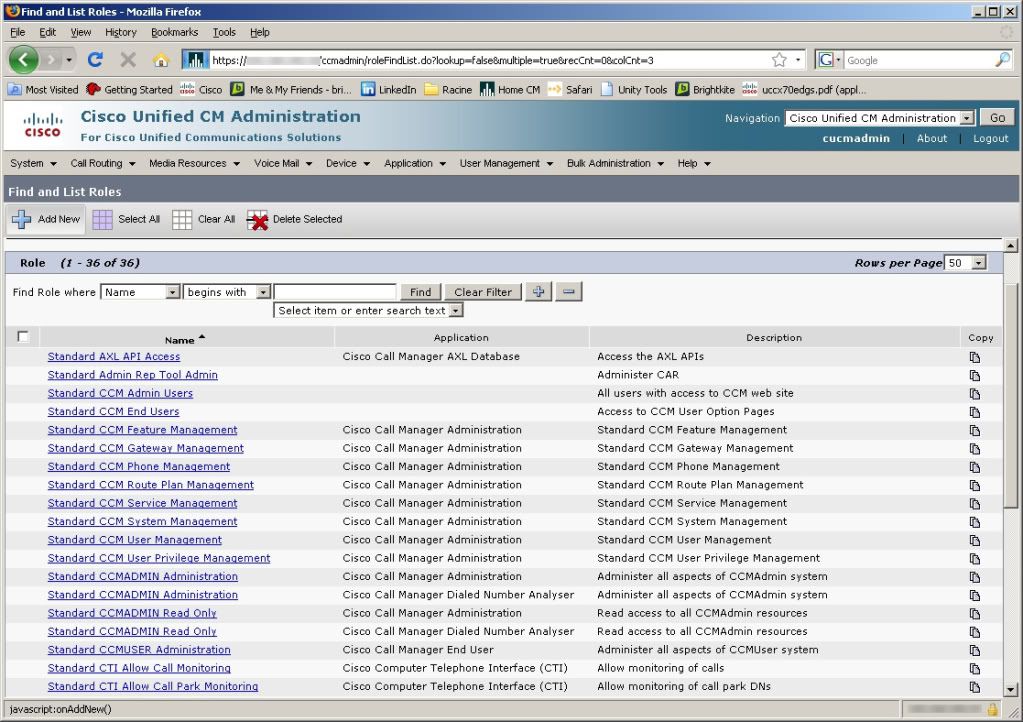
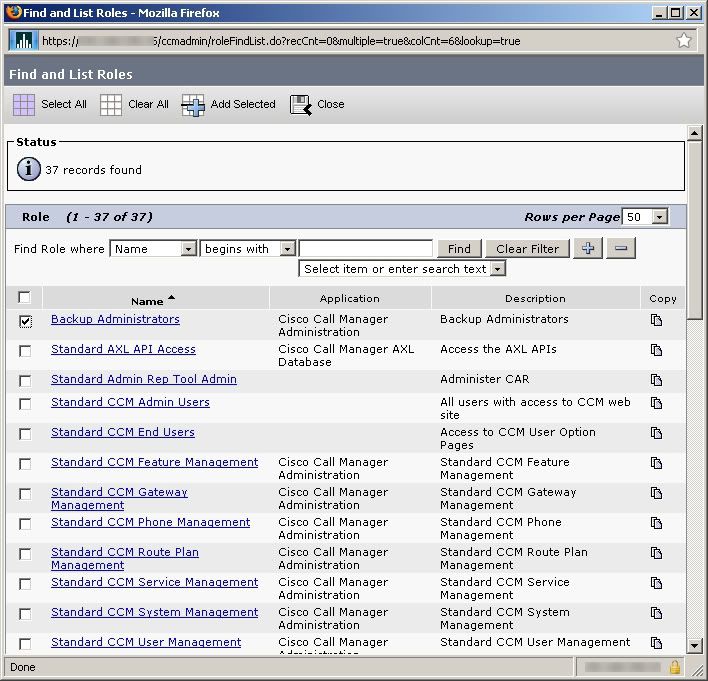
From the Find and List Roles screen, chose Add New.
Choose an application.
Name the role
Assign the permissions and save the role.
Create any other roles that will be added to the group. Remember you can assign roles from multiple applications to a group, so you may create roles in several applications for a user group. When you have all the roles defined, create the user group.
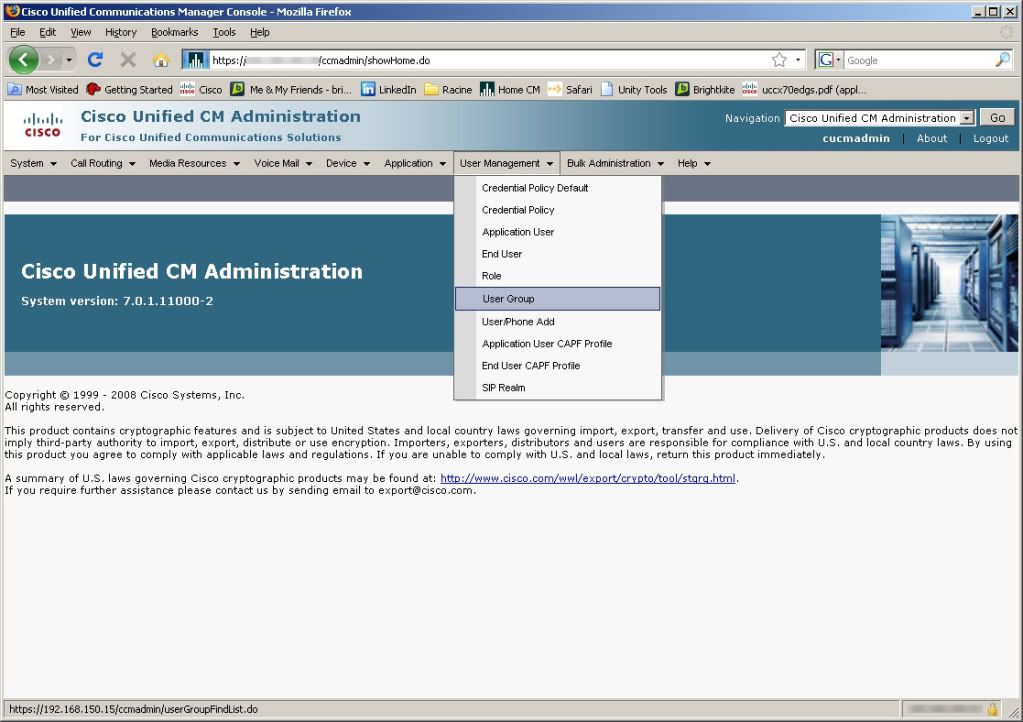
Create a Group and assign it roles
Choose User Groups from the User Management menu
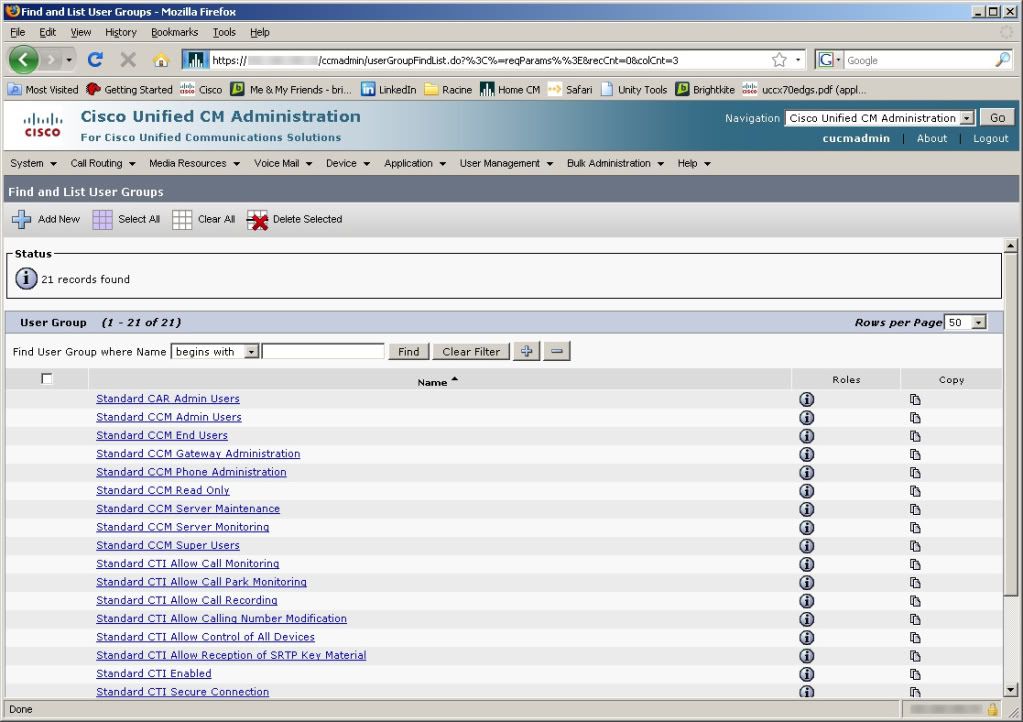
From the Find and List User Groups, choose Add New
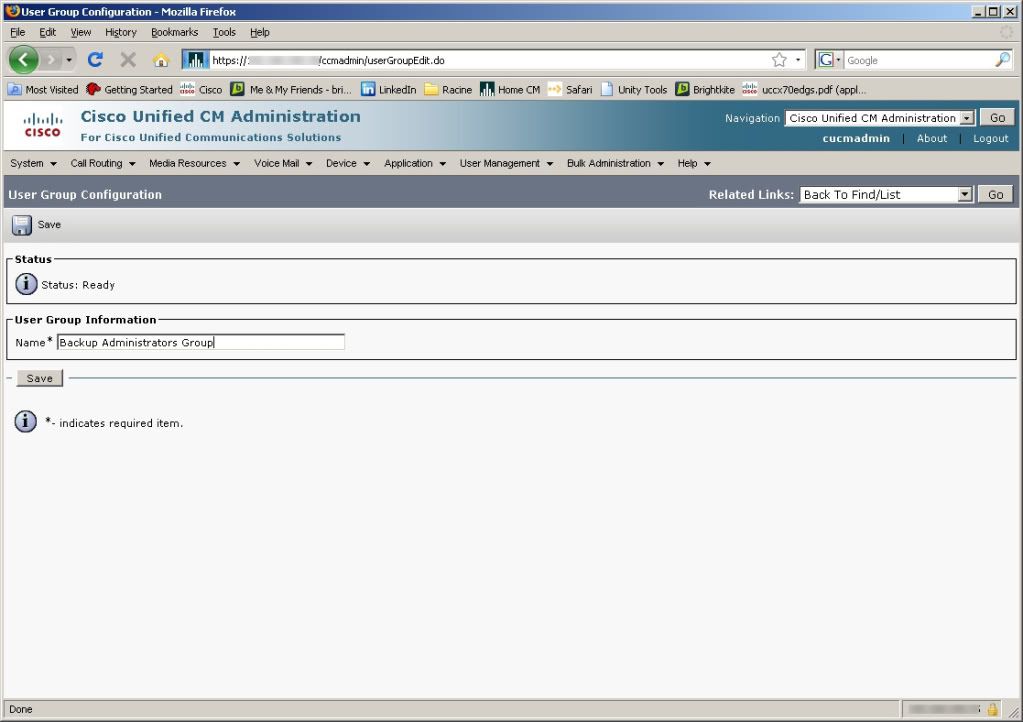
Create a name for the group, and click Save.
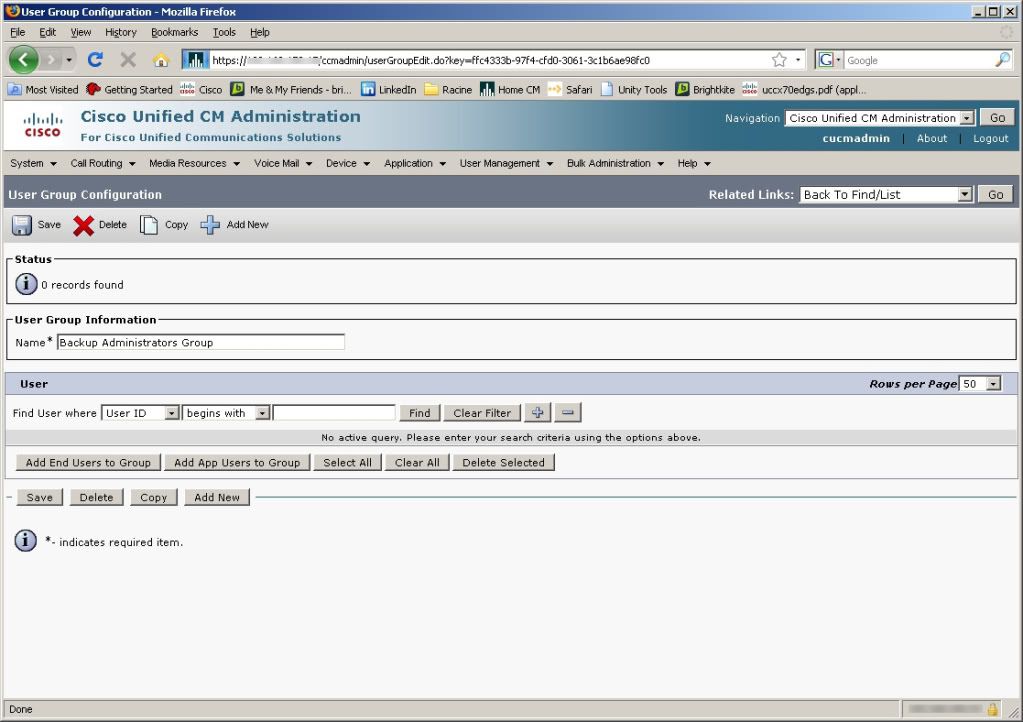
In the User Group Configuration screen, Click Add End Users to Group or Add Application Users to Group
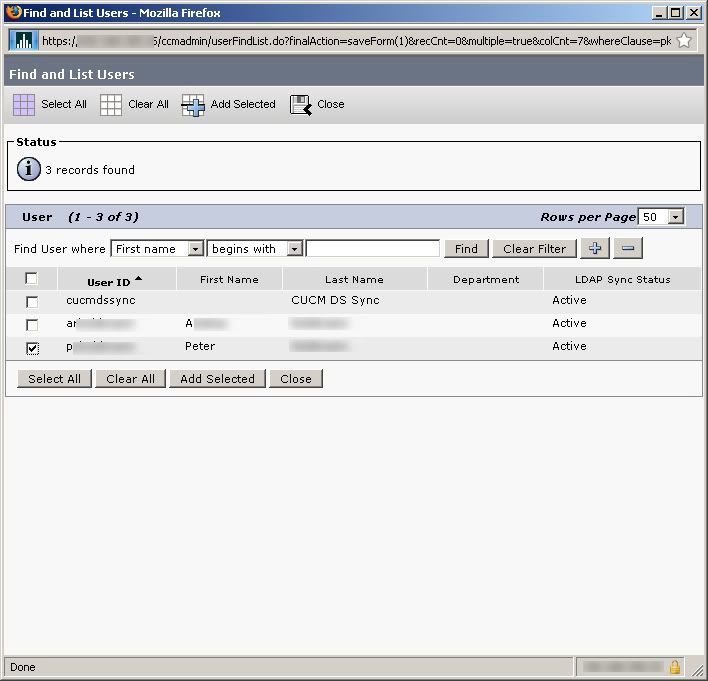
In the Find and List Users screen, select the users you want to add to the group, and click Add Selected when you are done.
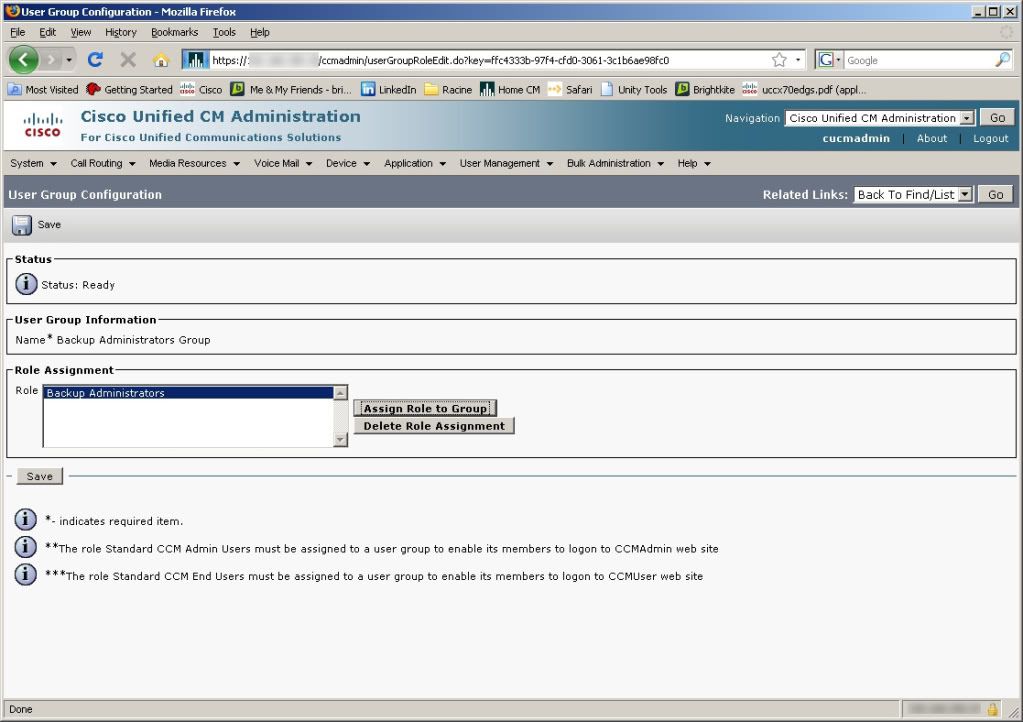
To assign roles to the group, return to the Find and List User Groups screen, and click the Circled “i” int the Roles column next to the group name to assign roles to the group
On the User Group Configuration page, click Assign Roles to Group
On the Find and List Roles page, Select the roles you want to add, then click Add Selected when you are done.
A user can also be assigned to groups within the End User Configuration Page.
In conclusion, like many other parts of CUCM administration, Cisco uses a multi-layer configuration to assign permissions to users. While there may seem to be more configuration up front, it offers a great deal of scalability, and once configured correctly simplifies administration by allowing for very specific groups of user rights to be assigned.
The one area that I think could be improved would be some ability to assign right restricted to a subset of devices/users/etc. like you can assign OU permissions in Active Directory.
Pingback: Cisco Unified Contact Center Express (UCCX) Initial Setup | Route, Switch, Blog